How SolarWinds and PRTG Keep Your Network Running 24/7
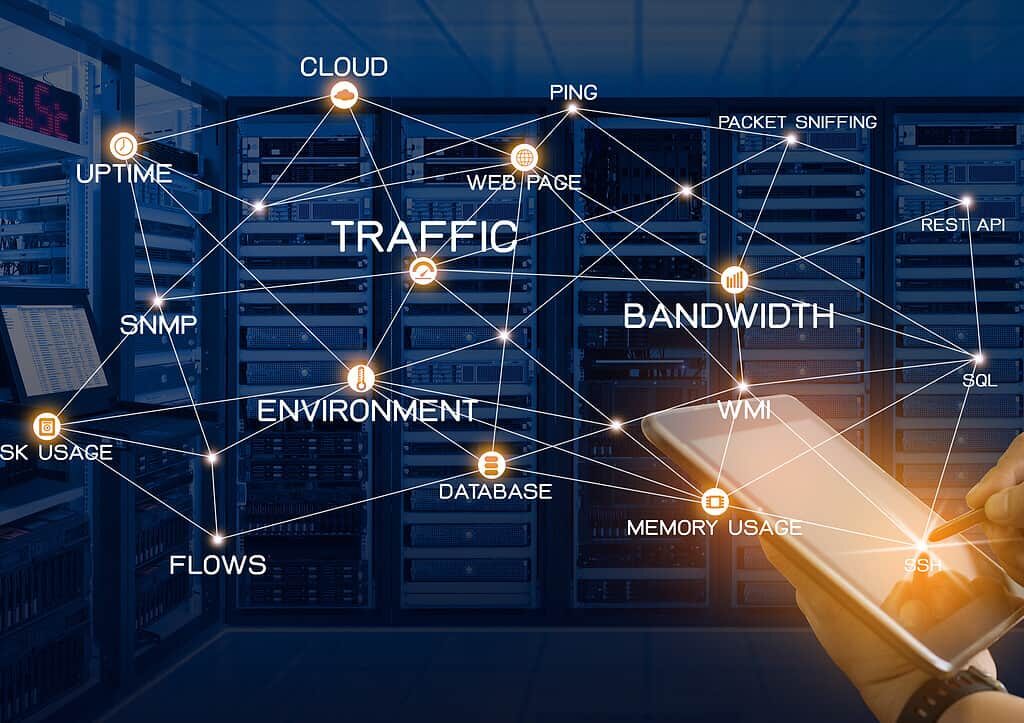
Introduction In today’s hyper-connected business world, network downtime is more than just an inconvenience — it’s a direct hit to productivity, revenue, and customer trust. Whether you manage a small office or a multinational IT infrastructure, ensuring continuous network performance is critical. Enter network monitoring tools like SolarWinds and PRTG Network Monitor. These platforms provide […]
How SolarWinds and PRTG Keep Your Network Running 24/7 Read More »